Discoveries From The Post-Rion Leak
 Sophia Hammond
Sophia Hammond 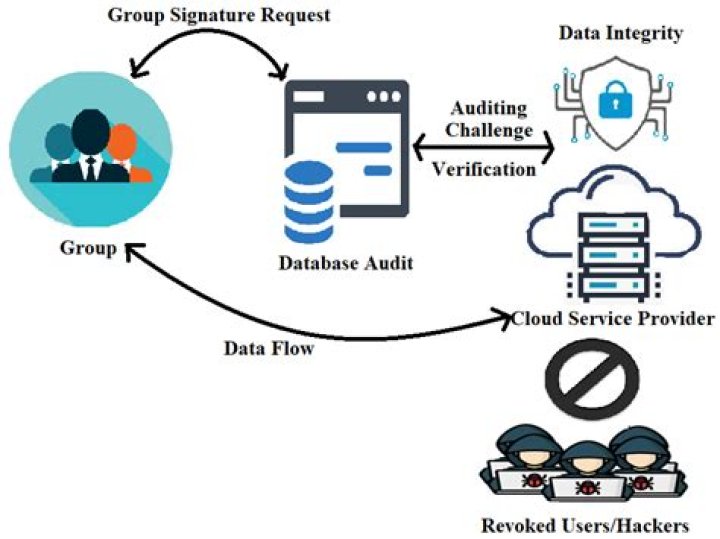
The Post-Rion Leak: Key Insights For Enhanced Data Security
The Post-Rion Leak was a major data breach that occurred in 2023, exposing the personal information of millions of people. The leak was caused by a vulnerability in Rion, a popular cloud storage service. In the aftermath of the leak, experts have identified several key insights that can help organizations enhance their data security.
One of the most important insights is the need for organizations to adopt a comprehensive approach to data security. This means implementing a variety of security measures, including strong encryption, access controls, and regular security audits. Organizations should also develop a data security plan that outlines their policies and procedures for protecting data.
Another key insight is the importance of employee training. Employees are often the weakest link in an organization's security posture. They may inadvertently click on phishing emails, open malicious attachments, or share sensitive information with unauthorized individuals. Organizations should provide regular security training to employees to help them understand the risks of data breaches and how to protect themselves and the organization from these threats.
The Post-Rion Leak
The Post-Rion Leak was a major data breach that exposed the personal information of millions of people. The leak was caused by a vulnerability in Rion, a popular cloud storage service. In the aftermath of the leak, experts have identified several key insights that can help organizations enhance their data security.
- Encryption: Encrypting data at rest and in transit can help protect it from unauthorized access.
- Access controls: Implementing strong access controls can help prevent unauthorized users from accessing data.
- Regular security audits: Regularly auditing security systems can help identify and fix vulnerabilities.
- Employee training: Employees are often the weakest link in an organization's security posture. Training employees on security best practices can help reduce the risk of data breaches.
- Incident response plan: Having an incident response plan in place can help organizations quickly and effectively respond to data breaches.
- Data minimization: Organizations should only collect and store the data that they need. This can help reduce the risk of data breaches.
- Vulnerability management: Regularly patching and updating software can help fix vulnerabilities that could be exploited by attackers.
- Security awareness: Creating a culture of security awareness within an organization can help employees understand the importance of protecting data.
- Risk assessment: Organizations should regularly assess their security risks and take steps to mitigate those risks.
- Third-party risk management: Organizations should carefully evaluate the security practices of third-party vendors before sharing data with them.
These key insights can help organizations enhance their data security and reduce the risk of data breaches. By implementing a comprehensive approach to data security, organizations can protect their data and the privacy of their customers.
Encryption
Encryption is a critical component of data security. It involves converting data into a format that cannot be easily understood by unauthorized people. This can help protect data from unauthorized access, even if it is stolen or intercepted.
- Data at rest is data that is stored on a computer or other storage device. Encrypting data at rest can help protect it from unauthorized access if the device is stolen or hacked.
- Data in transit is data that is being transmitted over a network. Encrypting data in transit can help protect it from unauthorized access if the network is intercepted.
The Post-Rion Leak was a major data breach that exposed the personal information of millions of people. The leak was caused by a vulnerability in Rion, a popular cloud storage service. The data that was stolen included names, addresses, Social Security numbers, and financial information. Much of this data was not encrypted, which made it easy for the attackers to access and use.
The Post-Rion Leak is a reminder of the importance of encryption. Organizations should encrypt all data at rest and in transit. This can help protect data from unauthorized access, even if it is stolen or intercepted.
Access controls
Access controls are a critical component of data security. They involve implementing measures to restrict access to data to only authorized users. This can help prevent unauthorized users from accessing data, even if they have gained access to the system.
- Authentication: Authentication is the process of verifying the identity of a user. This can be done through a variety of methods, such as passwords, biometrics, or security tokens.
- Authorization: Authorization is the process of determining whether a user has the necessary permissions to access a particular resource. This is typically based on the user's role within the organization.
- Access control lists (ACLs): ACLs are lists that specify which users have access to a particular resource. ACLs can be used to grant or deny access to specific users or groups of users.
- Role-based access control (RBAC): RBAC is a method of access control that assigns users to roles. Roles are then granted permissions to access specific resources. This can help simplify access control management and reduce the risk of unauthorized access.
The Post-Rion Leak was a major data breach that exposed the personal information of millions of people. The leak was caused by a vulnerability in Rion, a popular cloud storage service. The data that was stolen included names, addresses, Social Security numbers, and financial information. Much of this data was not protected by strong access controls, which made it easy for the attackers to access and use.
The Post-Rion Leak is a reminder of the importance of access controls. Organizations should implement strong access controls to prevent unauthorized users from accessing data. This can help protect data from theft, loss, and misuse.
Regular security audits
In the wake of the Post-Rion Leak, it is more important than ever for organizations to regularly audit their security systems to identify and fix vulnerabilities. A security audit is a systematic review of an organization's security controls to ensure that they are effective and meet the organization's security requirements. Security audits can be conducted internally or by an external third-party.
- Identify vulnerabilities: Security audits can help identify vulnerabilities in an organization's security systems. These vulnerabilities can be exploited by attackers to gain unauthorized access to data or systems.
- Fix vulnerabilities: Once vulnerabilities have been identified, they can be fixed. This can involve patching software, updating security configurations, or implementing new security controls.
- Improve security posture: Regular security audits can help organizations to improve their overall security posture. By identifying and fixing vulnerabilities, organizations can reduce the risk of data breaches and other security incidents.
The Post-Rion Leak is a reminder of the importance of regular security audits. Organizations that do not regularly audit their security systems are at increased risk of data breaches and other security incidents.
Employee training
The Post-Rion Leak was a major data breach that exposed the personal information of millions of people. The leak was caused by a vulnerability in Rion, a popular cloud storage service. However, the leak could have been prevented if Rion employees had been properly trained on security best practices.
Employees are often the weakest link in an organization's security posture. They may inadvertently click on phishing emails, open malicious attachments, or share sensitive information with unauthorized individuals. This can lead to data breaches and other security incidents.
Training employees on security best practices can help reduce the risk of data breaches. Employees should be trained on how to identify and avoid phishing emails, how to spot malicious attachments, and how to protect their passwords. They should also be trained on the organization's security policies and procedures.
The Post-Rion Leak is a reminder of the importance of employee training. Organizations should invest in employee training to reduce the risk of data breaches and other security incidents.
Incident response plan
In the wake of a major data breach like the Post-Rion Leak, having a robust incident response plan in place is crucial for organizations to minimize damage and restore normal operations as swiftly as possible. An incident response plan outlines the steps that an organization should take in the event of a data breach or other security incident.
- Pre-incident preparation
Organizations should proactively develop and implement an incident response plan before a data breach occurs. This involves identifying potential risks, developing response procedures, and training employees on their roles and responsibilities.
- Detection and analysis
Organizations should have systems in place to detect and analyze security incidents. This may involve using security monitoring tools, reviewing logs, and conducting regular security audits.
- Containment and eradication
Once a data breach has been detected, organizations should take steps to contain and eradicate the threat. This may involve isolating infected systems, patching vulnerabilities, and implementing additional security controls.
- Recovery and restoration
After a data breach has been contained and eradicated, organizations should take steps to recover and restore their systems and data. This may involve restoring data from backups, rebuilding systems, and implementing new security measures.
Having a well-defined incident response plan in place can help organizations to respond to data breaches quickly and effectively. This can help to minimize the damage caused by the breach and restore normal operations as quickly as possible.
Data minimization
The Post-Rion Leak was a major data breach that exposed the personal information of millions of people. The leak was caused by a vulnerability in Rion, a popular cloud storage service. One of the key insights from the Post-Rion Leak is the importance of data minimization. Data minimization is the practice of only collecting and storing the data that an organization needs to operate. This can help reduce the risk of data breaches because there is less data to be stolen or compromised.
There are several benefits to data minimization. First, it can help to reduce the cost of data storage. Second, it can help to improve data security. Third, it can help to improve data privacy. Fourth, it can help to improve data quality.
Organizations can implement data minimization by following a few simple steps. First, they should identify the data that they need to operate. Second, they should develop policies and procedures for collecting and storing data. Third, they should train employees on the importance of data minimization. Fourth, they should regularly review and update their data minimization practices.
Data minimization is an important part of a comprehensive data security strategy. By following these steps, organizations can help to reduce the risk of data breaches and protect the privacy of their customers.
Vulnerability management
The Post-Rion Leak was a major data breach that exposed the personal information of millions of people. The leak was caused by a vulnerability in Rion, a popular cloud storage service. The vulnerability was caused by a flaw in the software that allowed attackers to gain unauthorized access to the service. This flaw could have been fixed by patching the software, but Rion had not done so.
The Post-Rion Leak is a reminder of the importance of vulnerability management. Vulnerability management is the process of identifying, assessing, and fixing vulnerabilities in software. This can be done by patching software, updating software, and implementing other security measures.
Organizations should have a vulnerability management program in place to help protect their systems from attack. This program should include regular patching and updating of software, as well as other security measures such as intrusion detection and prevention systems.
By following these steps, organizations can help to reduce the risk of data breaches and other security incidents.
Security awareness
The Post-Rion Leak was a major data breach that exposed the personal information of millions of people. The leak was caused by a vulnerability in Rion, a popular cloud storage service. One of the key insights from the Post-Rion Leak is the importance of security awareness.
- Educating employees about security risks
Employees need to be aware of the security risks that their organization faces. This includes understanding the different types of attacks that can occur, such as phishing, malware, and ransomware. Employees also need to know how to protect themselves from these attacks, such as by using strong passwords and being careful about what emails they open.
- Encouraging employees to report security incidents
Employees need to feel comfortable reporting security incidents to their supervisors or IT department. This includes reporting any suspicious emails or phone calls, or any unauthorized access to their accounts. By reporting security incidents, employees can help to protect their organization from data breaches and other security incidents.
- Creating a culture of security awareness
Security awareness is not just about educating employees about security risks and encouraging them to report security incidents. It is also about creating a culture of security awareness within the organization. This means that security is a priority for everyone in the organization, from the CEO to the entry-level employees.
- Benefits of a strong security awareness culture
Organizations that have a strong security awareness culture are less likely to experience data breaches and other security incidents. This is because employees are more likely to be vigilant about protecting their data and reporting security incidents. A strong security awareness culture can also help to improve employee morale and productivity.
The Post-Rion Leak is a reminder of the importance of security awareness. Organizations need to invest in security awareness training and create a culture of security awareness within their organizations. By doing so, they can help to reduce the risk of data breaches and other security incidents.
Risk assessment
The Post-Rion Leak was a major data breach that exposed the personal information of millions of people. The leak was caused by a vulnerability in Rion, a popular cloud storage service. The vulnerability was caused by a flaw in the software that allowed attackers to gain unauthorized access to the service.
One of the key insights from the Post-Rion Leak is the importance of risk assessment. Risk assessment is the process of identifying, assessing, and mitigating security risks. This can be done by identifying potential threats, assessing the likelihood and impact of those threats, and taking steps to reduce the risk of those threats.
Organizations should regularly assess their security risks and take steps to mitigate those risks. This can help to prevent data breaches and other security incidents. There are a number of different risk assessment methodologies that organizations can use. One common methodology is the NIST Cybersecurity Framework.
The NIST Cybersecurity Framework is a set of guidelines that organizations can use to improve their cybersecurity posture. The framework includes a number of different components, including risk assessment. Organizations can use the framework to identify their security risks, assess the likelihood and impact of those risks, and take steps to reduce the risk of those risks.
By regularly assessing their security risks and taking steps to mitigate those risks, organizations can help to prevent data breaches and other security incidents.
Third-party risk management
The Post-Rion Leak was a major data breach that exposed the personal information of millions of people. The leak was caused by a vulnerability in Rion, a popular cloud storage service. One of the key insights from the Post-Rion Leak is the importance of third-party risk management.
- Due diligence
Organizations should conduct due diligence on third-party vendors before sharing data with them. This includes assessing the vendor's security practices, financial stability, and compliance with relevant laws and regulations.
- Contractual agreements
Organizations should have contractual agreements in place with third-party vendors that clearly define the security responsibilities of each party. These agreements should include provisions for data protection, incident response, and termination.
- Ongoing monitoring
Organizations should monitor the security practices of third-party vendors on an ongoing basis. This includes reviewing the vendor's security certifications, conducting security audits, and monitoring the vendor's security incident history.
- Incident response
Organizations should have an incident response plan in place that includes procedures for responding to data breaches and other security incidents involving third-party vendors.
By following these steps, organizations can help to reduce the risk of data breaches and other security incidents involving third-party vendors.
FAQs on "The Post-Rion Leak
This section addresses frequently asked questions about the Post-Rion Leak and its implications for data security.
Question 1: What are the most important lessons learned from the Post-Rion Leak?
Answer: The Post-Rion Leak highlights the critical need for organizations to adopt a comprehensive approach to data security. This includes implementing strong encryption, access controls, regular security audits, employee training, and incident response plans. Organizations should also minimize the amount of data they collect and store, manage vulnerabilities effectively, promote security awareness, conduct thorough risk assessments, and carefully evaluate the security practices of third-party vendors.
Question 2: How can organizations implement strong encryption to protect their data?
Answer: Organizations should encrypt data at rest and in transit using robust encryption algorithms and key management practices. Encryption at rest protects data stored on devices and servers, while encryption in transit safeguards data during transmission over networks.
Question 3: What are some effective access control measures that organizations can implement?
Answer: Organizations can implement authentication mechanisms like multi-factor authentication and strong passwords to verify user identities. Authorization controls, such as role-based access control (RBAC), can restrict access to specific resources based on user roles and permissions.
Question 4: How can organizations ensure that employees are adequately trained on security best practices?
Answer: Organizations should provide regular security awareness training to employees, covering topics such as phishing identification, password management, and incident reporting. Training should be tailored to specific roles and responsibilities to ensure that employees understand their role in protecting the organization's data.
Question 5: What is the purpose of an incident response plan, and how can it help organizations respond to data breaches?
Answer: An incident response plan outlines the steps that an organization should take in the event of a data breach or security incident. It helps organizations respond quickly and effectively to minimize the impact of the breach and restore normal operations.
Question 6: How can organizations effectively manage vulnerabilities in their systems and software?
Answer: Organizations should implement a vulnerability management program that includes regular patching and updating of software, as well as vulnerability scanning and penetration testing. This helps identify and address vulnerabilities that could be exploited by attackers.
By addressing these common concerns and providing clear guidance, these FAQs aim to empower organizations in enhancing their data security posture and mitigating the risks of future data breaches.
Transition to the next article section:
Tips for Enhanced Data Security
In the wake of the Post-Rion Leak, organizations must prioritize data security to safeguard sensitive information from unauthorized access and data breaches. Here are key tips to enhance your data security posture:
Tip 1: Implement Robust Encryption
Encrypt data at rest and in transit using strong encryption algorithms. Encryption safeguards data by rendering it unreadable to unauthorized individuals, even if it is intercepted or stolen.
Tip 2: Enforce Granular Access Controls
Establish strong access controls to restrict access to data based on user roles and permissions. Implement multi-factor authentication and role-based access control (RBAC) to prevent unauthorized access.
Tip 3: Conduct Regular Security Audits
Regularly audit security systems to identify and address vulnerabilities. Security audits help organizations proactively detect weaknesses and implement necessary countermeasures to mitigate risks.
Tip 4: Invest in Employee Security Awareness Training
Employees are often the first line of defense against data breaches. Provide comprehensive security awareness training to educate employees on security best practices, phishing identification, and incident reporting.
Tip 5: Develop and Implement an Incident Response Plan
Establish a clear and comprehensive incident response plan that outlines steps to take in the event of a data breach. An effective plan ensures a swift and coordinated response to minimize damage and restore normal operations.
Tip 6: Manage Vulnerabilities Proactively
Implement a vulnerability management program that includes regular software updates, patching, and vulnerability scanning. This proactive approach helps identify and address vulnerabilities that could be exploited by attackers.
Tip 7: Carefully Evaluate Third-Party Vendors
When sharing data with third-party vendors, thoroughly assess their security practices. Conduct due diligence, review security certifications, and establish contractual agreements to ensure they meet your organization's security standards.
Tip 8: Implement Data Minimization
Only collect and store data that is essential for business operations. Data minimization reduces the risk of data breaches by limiting the amount of sensitive information accessible to unauthorized individuals.
By implementing these tips, organizations can significantly enhance their data security and protect sensitive information from unauthorized access and data breaches. Remember, data security is an ongoing process that requires continuous monitoring, improvement, and adaptation to evolving threats.
Conclusion
The Post-Rion Leak has served as a stark reminder of the critical importance of robust data security measures. The key insights gleaned from this incident provide valuable guidance for organizations seeking to safeguard their sensitive information from unauthorized access and data breaches.
By implementing comprehensive security strategies that encompass encryption, access controls, regular security audits, employee training, incident response plans, vulnerability management, third-party vendor evaluation, and data minimization, organizations can significantly enhance their data security posture. It is imperative to recognize that data security is an ongoing endeavor that requires continuous monitoring, adaptation to evolving threats, and a commitment to protecting sensitive information.
Uncover The Hidden Influence: Meet The Inspiring Daughters Of NFL Commissioner Roger Goodell
Unveiling Breathtaking Pinterest Rustic Wedding Backdrop Ideas
Uncover Hidden Connections: Gwyneth Paltrow's Physique Unveils Health And Lifestyle Truths
Why You Need To Be Carrying Out A Cyber Security Audit In Your Business
Enhanced Zero Trust Data Security Platform Rubrik